Snyk vs Aqua Security: Developer-First Security vs Cloud-Native Platform (2026)
Snyk vs Aqua Security - developer-first SAST and SCA vs cloud-native container and runtime security. Pricing, SBOM, and shift-left DevSecOps comparison.
Published:
Last Updated:
Quick Verdict
Snyk and Aqua Security are not competing products in the traditional sense - they occupy different positions on the application security lifecycle and were built for different buyers with different problems. Understanding where each tool lives in the security stack is the key to making the right decision for your team.
Snyk is a developer-first security platform built to shift security left. It meets developers where they are - in the IDE, in the pull request, in the CLI - and surfaces security findings in a language and workflow developers already understand. Its five products (Snyk Code for SAST, Snyk Open Source for SCA, Snyk Container for container image scanning, Snyk IaC for infrastructure as code, and Snyk Cloud for runtime cloud posture) cover the full pre-deployment security surface. A named Leader in the 2025 Gartner Magic Quadrant for Application Security Testing, Snyk has over 4,500 organizational customers and is used by more than 400,000 developers globally. Its Team plan starts at $25 per developer per month.
Aqua Security is an enterprise cloud-native security platform built to protect containerized and Kubernetes-based applications across their entire lifecycle - from code to container to runtime. Founded in 2015 and headquartered in Boston, Aqua pioneered container runtime security at a time when Docker and Kubernetes were transforming how software was deployed. Unlike Snyk’s developer-facing positioning, Aqua’s primary buyers are security teams and DevSecOps engineers responsible for production security posture. Aqua does not publish pricing; enterprise contracts typically start at $25,000 to $40,000 per year and scale to hundreds of thousands of dollars for large multi-cloud deployments.
Choose Snyk if: your team is developer-centric, you want shift-left security integrated into the IDE and PR workflow, your primary concern is code vulnerabilities and dependency risk, and you need a tool that developers will actually adopt without significant friction or operational overhead.
Choose Aqua Security if: your organization runs containerized workloads at scale in Kubernetes, you need runtime security enforcement alongside pre-deployment scanning, you have a dedicated DevSecOps function that can manage an enterprise security platform, and your compliance requirements extend to runtime behavior monitoring.
The honest answer for most teams: if you are comparing these two tools, you are likely a developer or DevSecOps lead evaluating how to build a comprehensive security program. The answer is usually Snyk for developer-facing security (SAST, SCA, container image scanning in the pipeline) combined with a runtime security tool for production enforcement. Whether that runtime tool is Aqua, Falco, or another platform depends on your infrastructure complexity and budget. Aqua as a standalone alternative to Snyk only makes sense if you need Aqua’s runtime and Kubernetes-native capabilities and are willing to accept weaker developer workflow integration for pre-deployment code scanning.
At-a-Glance Comparison
| Category | Snyk | Aqua Security |
|---|---|---|
| Primary buyer | Developers and security engineers | Security teams and DevSecOps engineers |
| Founded | 2015 | 2015 |
| SAST (code scanning) | Yes - Snyk Code with DeepCode AI (19+ languages) | Yes - Aqua Code module (less developer-centric) |
| SCA (dependency scanning) | Yes - Snyk Open Source with reachability analysis | Yes - basic SCA capability |
| Container image scanning | Yes - Snyk Container (pre-deployment) | Yes - registry and CI/CD scanning (pre-deployment) |
| Container runtime security | No | Yes - eBPF-based runtime enforcement |
| Kubernetes admission control | No | Yes - policy-based pod admission |
| IaC scanning | Yes - Snyk IaC (Terraform, K8s, CloudFormation, ARM) | Yes - Aqua IaC (Terraform, Helm, K8s manifests) |
| CSPM (cloud posture) | Limited - Snyk Cloud | Yes - AWS, Azure, GCP posture management |
| SBOM generation | Yes - CycloneDX and SPDX via CLI/API | Yes - supply chain module, broader container coverage |
| Software supply chain security | Partial - SCA and license compliance | Yes - dedicated supply chain security module |
| AI-powered fix suggestions | Yes - DeepCode AI Fix in Snyk Code | Limited - not a primary feature |
| IDE integration | Yes - VS Code, JetBrains (real-time scanning) | No IDE plugin |
| PR / merge gating | Yes - GitHub, GitLab, Bitbucket, Azure DevOps | Yes - CI/CD integration with policy enforcement |
| Free tier | Yes - 100 SAST tests/month, limited SCA/container | No standard free tier (trials available) |
| Pricing model | Per developer ($25/dev/month for Team plan) | Custom enterprise pricing (node/workload-based) |
| Typical entry cost | $125/month (5 devs on Team plan) | $25,000 to $40,000/year (enterprise minimum) |
| Developer adoption friction | Low - integrates into existing tools | High - requires agent deployment and security team management |
| Gartner positioning | Magic Quadrant Leader for AST (2025) | Strong enterprise cloud-native security vendor |
| Best for | Developer teams, shift-left security | Enterprise DevSecOps, Kubernetes-at-scale, runtime security |
What Is Snyk?
Snyk is a developer security platform that consolidates application security scanning across five domains under a single developer-facing interface. The platform’s positioning as “developer-first” is not marketing - it reflects a fundamental architectural choice to integrate security into developer tools and workflows rather than create a separate security team portal.
The five Snyk products work together to cover the full pre-deployment attack surface:
Snyk Code is the SAST (Static Application Security Testing) engine, powered by DeepCode AI. It performs single-file and interfile data flow analysis across 19+ languages to detect injection vulnerabilities, authentication weaknesses, cryptographic issues, and other code-level security problems. The DeepCode AI Fix feature generates contextually relevant remediation suggestions trained on curated human-made fixes, not generic LLM output. Snyk Code runs in real time in VS Code and JetBrains IDEs, in PR checks across all four major git platforms, and in CI/CD pipelines. Named a Gartner Magic Quadrant Leader for Application Security Testing in 2025, Snyk Code benchmarks as 6.7x faster in median scan time than SonarQube.
Snyk Open Source is the SCA engine. It scans dependency manifests (package.json, requirements.txt, pom.xml, go.mod, Gemfile, and others) to identify known CVEs in open-source packages. The key differentiator is reachability analysis - Snyk determines whether vulnerable code paths in your dependencies are actually called by your application, cutting through the noise of transitive dependency alerts that have no real-world impact. Snyk’s vulnerability database updates within 24 hours of new CVE disclosures, compared to the weekly cycles of some competitors.
Snyk Container scans Docker images and container configurations for known vulnerabilities in base images and installed packages. It integrates with Docker Hub, Amazon ECR, Google Container Registry, and Azure Container Registry, providing visibility into vulnerabilities at the infrastructure layer before containers are deployed.
Snyk IaC scans Terraform, CloudFormation, Kubernetes manifests, and ARM templates for misconfigurations and security issues before they reach production - catching overly permissive IAM policies, unencrypted storage buckets, publicly exposed databases, and other common cloud security mistakes.
Snyk Cloud provides CSPM (Cloud Security Posture Management) capabilities for AWS, Azure, and GCP, checking deployed cloud resources against security best practices and compliance benchmarks.
For a full breakdown of Snyk’s capabilities, pricing, and integrations, see our Snyk Code review.
What Is Aqua Security?
Aqua Security is a cloud-native application security platform that secures containerized applications from development through production. Founded in 2015, Aqua pioneered Kubernetes-native security at a time when the industry was still figuring out how to treat containers as a first-class security surface. Today, Aqua serves enterprise organizations running complex containerized architectures across AWS, Azure, and Google Cloud.
Aqua’s platform is organized around four security pillars that together cover the cloud-native application lifecycle:
Aqua Code covers code security - SAST scanning for source code vulnerabilities and secret detection across repositories. This is Aqua’s newest and least mature module compared to its container-centric capabilities. It integrates with GitHub, GitLab, Bitbucket, and Azure DevOps for PR-level scanning, but lacks the developer-first ergonomics of Snyk Code’s IDE plugins and AI-powered fix suggestions.
Aqua Supply Chain Security is where Aqua differentiates sharply from Snyk. This module provides end-to-end software supply chain protection: scanning for malicious packages injected into open-source registries, detecting tampering in CI/CD pipelines, enforcing SLSA (Supply Chain Levels for Software Artifacts) compliance, generating and analyzing SBOMs (Software Bills of Materials), and providing artifact signing and verification. For organizations operating under US government supply chain security mandates or SLSA compliance requirements, Aqua’s supply chain module addresses requirements that Snyk does not fully cover.
Aqua Cloud Security provides CSPM (Cloud Security Posture Management) with continuous configuration scanning across AWS, Azure, and GCP. It benchmarks cloud configurations against CIS controls, detects IAM misconfigurations, identifies exposed storage and databases, and provides remediation guidance. The cloud security module overlaps with Snyk Cloud but generally provides more depth in multi-cloud posture management for organizations with complex cloud estates.
Aqua Runtime Security is Aqua’s most distinctive and differentiated capability - and the capability that Snyk entirely lacks. Aqua deploys lightweight eBPF-based enforcement agents on Kubernetes nodes that monitor running containers in real time. At runtime, Aqua can:
- Detect behavioral anomalies when a container deviates from its expected baseline behavior (drift detection)
- Block execution of unauthorized binaries or file modifications that were not present in the original container image
- Enforce network policies at the container level, limiting communication to explicitly allowed connections
- Alert on unusual system calls, privilege escalations, and suspicious process activity
- Provide forensic data on container activity for incident investigation
This runtime enforcement layer is where Aqua provides security value that no pre-deployment scanner - including Snyk - can replicate. A container image that passes all pre-deployment scans can still be compromised at runtime through a zero-day exploit, a misconfigured environment variable, or a supply chain attack that post-dates the initial scan. Aqua’s runtime protection catches these post-deployment threats and can respond to them automatically.
Kubernetes-Native Controls are woven throughout Aqua’s platform. Aqua integrates with Kubernetes admission controllers to enforce policies at pod scheduling time - if a container image does not meet Aqua’s security policies (unsigned image, critical CVEs, failed hardening checks), Aqua can block the pod from being scheduled entirely. This Kubernetes-native enforcement layer creates a hard security boundary that policy enforcement from a separate scanning tool cannot provide.
Feature-by-Feature Breakdown
SAST: Code Vulnerability Detection
Snyk Code is the clear winner for developer-facing SAST. The DeepCode AI engine provides interfile data flow analysis across 19+ languages, detecting complex vulnerability patterns like taint flows from user input to dangerous sinks across multiple files and function boundaries. The AI-powered fix suggestions are trained on curated human-made remediation examples, not generic LLM output, which results in relevant, implementable fixes rather than hallucinated code. Developers interact with Snyk Code directly in VS Code and JetBrains IDEs with real-time scanning, in GitHub/GitLab/Bitbucket/Azure DevOps PR checks with inline annotations, and in CLI scans that complete in seconds to minutes.
Aqua Code provides SAST as a secondary capability. Its code scanning identifies OWASP Top 10 vulnerabilities, secret exposure, and common injection patterns through repository integration. The analysis runs as part of the CI/CD pipeline or repository monitoring, not in real time in the IDE. Aqua does not offer the AI-powered fix suggestions, the developer-friendly vulnerability explanations, or the IDE plugins that make Snyk Code genuinely easy for developers to act on. Aqua’s code scanning is designed to give security teams visibility into code risk, not to help individual developers remediate issues faster.
Verdict: Snyk wins on SAST. For developer-facing code security scanning, Snyk Code’s DeepCode AI engine, IDE integration, and AI-powered remediation are meaningfully better than Aqua’s code module for development teams. Security teams that need governance-level code scanning as one layer in a broader security program may find Aqua’s integrated view more useful despite the weaker developer experience.
SCA: Dependency and Open-Source Risk
Snyk Open Source is one of the strongest SCA products available. Its vulnerability database covers all major package ecosystems - npm, PyPI, Maven, NuGet, Go modules, RubyGems, Composer, Cargo, and others - with updates within 24 hours of new CVE disclosures. The reachability analysis capability is Snyk’s most differentiated SCA feature: rather than alerting on every vulnerable package in the dependency tree, Snyk traces code execution paths to determine whether the vulnerable function is actually called by your application. This dramatically reduces alert fatigue by focusing attention on vulnerabilities with real exploit potential.
Aqua Security provides SCA as part of its supply chain security module, but SCA is not Aqua’s primary strength. Aqua’s dependency scanning is more focused on software bill of materials (SBOM) generation and supply chain integrity verification than on the developer-centric alerting and automated fix PR workflow that Snyk provides. Aqua does not have a reachability analysis capability comparable to Snyk’s.
Verdict: Snyk wins on SCA. The combination of a comprehensive vulnerability database, reachability analysis, and automatic fix PRs makes Snyk Open Source the stronger SCA product for development teams managing open-source dependency risk.
Container Security: Image Scanning and Runtime Protection
This is the most nuanced dimension in the comparison, and where the two tools serve fundamentally different needs.
Pre-deployment image scanning is a tie. Both Snyk Container and Aqua Security scan container images for known CVEs in base images and installed packages. Both integrate with major container registries. Both can be embedded into CI/CD pipelines to gate deployments on security findings. The quality of pre-deployment scanning is comparable; the choice between them for image scanning alone is primarily a question of how the findings surface in your workflow (developer-friendly Snyk vs security-team-oriented Aqua) and what other capabilities you need from the same platform.
Runtime security is Aqua’s exclusive territory. Snyk Container does not provide runtime protection. Once a container is deployed and running, Snyk has no visibility into what happens inside it. Aqua’s eBPF-based runtime enforcement agent continuously monitors running containers, builds behavioral baselines, detects anomalies, and can block malicious activity in real time. For organizations that have experienced container escapes, cryptomining attacks in Kubernetes clusters, or supply chain compromises that bypass pre-deployment scanning, this runtime layer is the difference between detecting an attack and being unaware of it entirely.
Kubernetes admission control is Aqua-exclusive. Snyk does not provide Kubernetes admission control. Aqua integrates with Kubernetes admission webhooks to evaluate pods against security policies before they are scheduled. If a container image fails Aqua’s security requirements (unscanned, unsigned, known critical CVEs), the pod is blocked from running in the cluster entirely. This creates a hard enforcement boundary that CI/CD-level gate checks cannot provide - a developer could theoretically bypass CI/CD gates, but they cannot bypass a properly configured admission controller.
Verdict: Snyk wins for pre-deployment image scanning in developer pipelines. Aqua wins comprehensively for runtime security and Kubernetes-native enforcement. The choice depends entirely on whether you need runtime protection. If you do not run Kubernetes or containerized workloads at scale, Snyk Container is the simpler, better-integrated option. If runtime security is a requirement, Aqua provides capabilities that Snyk simply does not have.
Supply Chain Security and SBOM
Software supply chain security has become a compliance and operational priority following high-profile attacks like the SolarWinds compromise and Log4Shell. Both tools address supply chain security, but from different angles.
Snyk approaches supply chain security through SCA and license compliance. Snyk Open Source identifies known CVEs in open-source dependencies, detects packages with restrictive licenses (GPL, LGPL) that could create legal exposure, and can alert on newly published vulnerabilities in packages you already use. Snyk generates SBOMs in CycloneDX and SPDX formats through its CLI and API. However, Snyk does not detect malicious packages injected into registries (as opposed to packages with known CVEs), does not verify artifact signatures, and does not enforce SLSA supply chain compliance levels.
Aqua Security has a dedicated supply chain security module that goes significantly further. Aqua’s supply chain capabilities include: detecting malicious packages in open-source registries before they are installed, verifying integrity of artifacts and packages in CI/CD pipelines, enforcing SLSA compliance levels (SLSA 1 through 4), signing and verifying container images and build artifacts with Cosign and Notary, providing end-to-end audit trails of how artifacts move from source code to deployment, and generating comprehensive SBOMs that cover the full container supply chain including base image layers and installed system packages.
For organizations with US government contracts that mandate SBOM compliance under Executive Order 14028, or for organizations implementing SLSA as part of their security program, Aqua’s supply chain module provides compliance evidence that Snyk does not generate. For most development teams without these specific requirements, Snyk’s SCA coverage is sufficient for open-source vulnerability management.
Verdict: Aqua wins on supply chain security breadth. For organizations that need SLSA compliance, artifact signing, registry monitoring for malicious packages, and comprehensive SBOMs covering the full container supply chain, Aqua’s dedicated supply chain security module is significantly more capable than Snyk’s SCA-focused approach.
IaC Security: Infrastructure Configuration Scanning
Both tools scan infrastructure-as-code configurations for security misconfigurations, with broadly comparable coverage of the major formats.
Snyk IaC scans Terraform, AWS CloudFormation, Kubernetes manifests, Helm charts, Azure ARM templates, and Docker Compose files. It surfaces findings in the developer workflow - in the Snyk IDE plugin, in PR checks, and in CLI scans - with the same developer-friendly UX as Snyk Code and Snyk Open Source. Snyk IaC tests are included in the free tier (300/month) and the Team plan.
Aqua IaC scanning covers Terraform, CloudFormation, Kubernetes manifests, and Helm charts, integrated into Aqua’s broader security platform rather than into the developer workflow. For organizations already running Aqua for container and runtime security, having IaC scanning in the same platform with correlated results across code, containers, and infrastructure provides a unified security view.
Verdict: Roughly equivalent on IaC coverage. Snyk IaC has better developer workflow integration and more transparent pricing. Aqua IaC provides better correlation with container and runtime security findings. Choose based on which workflow integration matters more for your team.
Developer Experience and Adoption
Developer adoption is one of the most underrated factors in application security tool selection. A tool that developers do not use - because it is too slow, too noisy, too complex, or lives in a separate portal - provides zero security value regardless of its technical capabilities.
Snyk is designed from the ground up for developer adoption. The free tier allows any developer to start scanning immediately without procurement or IT involvement. The VS Code and JetBrains plugins require a five-minute setup and provide real-time feedback in the tools developers already use. CLI scanning takes seconds. PR checks provide inline annotations at the specific line of code where the issue exists, with a clear severity rating and link to remediation guidance. AI-powered fix suggestions give developers a concrete starting point for remediation rather than leaving them to research the fix independently. Snyk’s G2 ease-of-use rating is 8.7 out of 10.
Aqua Security is designed for security team governance. Deploying Aqua in a Kubernetes cluster requires installing runtime enforcement agents, configuring security policies, integrating with the Kubernetes admission controller, and establishing image assurance policies. This is not a self-service five-minute setup - it requires DevSecOps expertise, infrastructure access, and typically a sales-assisted implementation process. Developers interact with Aqua primarily through CI/CD pipeline findings and security alerts generated by the platform. There is no IDE plugin that gives developers real-time feedback as they write code.
Verdict: Snyk wins decisively on developer experience. If your goal is developer adoption of security practices - developers who actually run scans, understand findings, and remediate issues - Snyk’s developer-first design is a meaningful practical advantage over Aqua’s security-team-centric approach.
Pricing Comparison
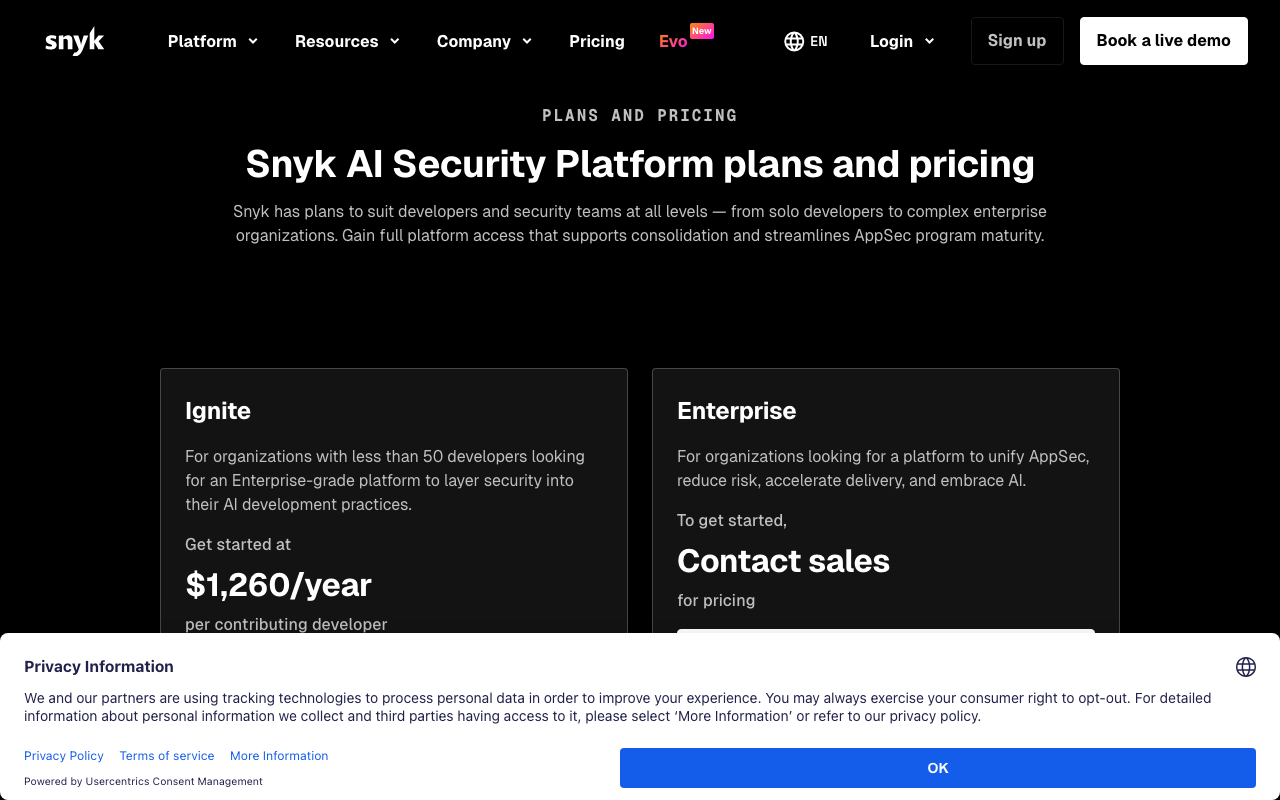
Snyk Pricing
| Plan | Price | Key Inclusions |
|---|---|---|
| Free | $0 | 100 SAST tests/month, 400 SCA tests/month, 300 IaC tests/month, 100 container tests/month |
| Team | $25/developer/month (min 5 devs) | Unlimited scans, DeepCode AI auto-fix, PR gating, Jira integration |
| Enterprise | Custom | SSO/SAML, custom policies, compliance reporting, reachability analysis, premium support |
At 10 developers on the Team plan, Snyk costs $2,500 per month or $30,000 per year. At 50 developers, the Team plan runs $15,000 per month or $180,000 per year before Enterprise pricing kicks in. Based on market data, 50-developer Enterprise deployments typically run $35,000 to $47,000 annually, and 100-developer deployments range from $67,000 to $90,000.
For the full breakdown of what drives Snyk’s costs at scale, see our Snyk pricing guide.
Aqua Security Pricing
Aqua does not publish pricing. All deployments require a sales conversation and custom quote. Based on market intelligence and publicly available information:
- Entry-level deployments (small Kubernetes clusters, limited node count): $25,000 to $40,000 per year
- Mid-market deployments (multiple clusters, moderate workload count): $50,000 to $150,000 per year
- Enterprise deployments (hundreds of nodes, full platform with runtime security, supply chain, CSPM): $150,000 to $500,000+ per year
Aqua’s pricing is typically based on the number of nodes or workloads rather than the number of developers. This can be advantageous for large development teams where per-developer pricing would be prohibitive, but it escalates quickly as Kubernetes infrastructure grows.
The pricing gap between the two tools is significant. Snyk’s Team plan at $25 per developer per month provides meaningful security coverage for development teams at an accessible price point. Aqua’s enterprise pricing model means no meaningful Aqua deployment is available for under $25,000 per year, which puts it out of reach for most teams under 50 to 100 developers.
Side-by-Side Cost at Scale
| Team / Infrastructure | Snyk Annual Cost | Aqua Annual Cost (estimated) | Notes |
|---|---|---|---|
| 10 developers, no Kubernetes | $2,500/yr (Team) | Not viable | Aqua minimum ~$25K/yr |
| 25 developers, small K8s cluster | ~$7,500/yr (Team) | $25K-$40K/yr | 3-5x cost premium for runtime security |
| 50 developers, medium K8s cluster | $35K-47K/yr (Enterprise) | $50K-$100K/yr | Converging cost as Snyk scales per-dev |
| 100 developers, large K8s | $67K-90K/yr (Enterprise) | $100K-$250K/yr | Aqua adds runtime value at this scale |
| 200+ devs, multi-cloud K8s | Custom | $250K-$500K+/yr | Different buyer, different use case |
Where CodeAnt AI Fits
For teams evaluating Snyk because they need developer-facing security scanning without the operational complexity or cost of an enterprise platform like Aqua, CodeAnt AI is worth considering as a third option. At $24/user/month for the Basic plan (AI code review) or $40/user/month for Premium (which adds SAST, secret detection, IaC security, and DORA metrics), CodeAnt AI provides meaningful security scanning coverage - OWASP Top 10 SAST, secret detection, IaC security - at a price point competitive with Snyk’s Team plan. For a 20-person team, CodeAnt AI Premium runs $9,600 per year versus approximately $6,000 per year for Snyk Team, but bundles AI-powered PR review, DORA metrics, and engineering dashboards that Snyk does not include.
CodeAnt AI does not offer runtime security or Kubernetes admission control, and its SCA depth does not match Snyk Open Source’s reachability analysis. But for teams whose primary need is code-level security scanning with developer-friendly UX, it is a genuine alternative to evaluate alongside Snyk.
Use Cases - When to Choose Each
Choose Snyk When
Your team is developer-centric and security friction is a concern. Snyk’s IDE plugins, sub-minute scan times, and AI-powered fix suggestions make it the easiest security platform for developers to adopt without coercion. If your primary challenge is getting developers to care about security rather than managing a complex security program, Snyk’s developer-first design is the right choice.
You need comprehensive pre-deployment coverage across code, dependencies, containers, and IaC. Snyk’s five products cover every pre-deployment security surface in a unified platform with consistent pricing and a single dashboard. For development teams that want “one security platform for everything before it ships,” Snyk delivers this more cleanly than most alternatives.
Your team is small to mid-size (5 to 100 developers) without a dedicated security function. Snyk’s self-service onboarding, free tier, and transparent $25/developer/month pricing make it accessible for teams that cannot run a procurement process or justify a six-figure security tooling budget. This is where Snyk and Aqua Security most clearly serve different buyers - Snyk works without enterprise security expertise; Aqua requires it.
You primarily write code rather than manage deployed infrastructure. Snyk’s security value is concentrated in the development phase. If your team’s security concern is “are we shipping vulnerable code and vulnerable dependencies,” Snyk answers that question comprehensively. If your concern is “what happens to our containers after they are deployed,” Snyk does not answer that question.
You want to integrate security into existing developer tools without adding a new portal. Snyk’s VS Code and JetBrains plugins, GitHub/GitLab/Bitbucket/Azure DevOps integrations, and CLI mean developers interact with security findings in tools they already use. There is no “log into the security platform” step in the developer workflow.
Choose Aqua Security When
You run Kubernetes at scale and need runtime security enforcement. This is the scenario where Aqua is irreplaceable. If you have had container escapes, cryptomining attacks in your cluster, or supply chain compromises that bypassed pre-deployment scanning, you need runtime protection that pre-deployment tools cannot provide. Aqua’s eBPF-based runtime enforcement and Kubernetes admission control are the most mature capabilities in the market for this use case.
You need SLSA compliance or software supply chain security beyond SCA. US government contractors, critical infrastructure operators, and organizations implementing formal supply chain security programs need SLSA compliance verification, artifact signing, pipeline integrity monitoring, and SBOM generation across the full container supply chain. Aqua’s supply chain security module addresses these requirements; Snyk’s SCA-based approach does not.
You have a dedicated DevSecOps function and can manage enterprise tooling. Aqua’s operational complexity - deploying runtime agents, configuring Kubernetes admission controllers, managing image assurance policies, tuning runtime behavioral baselines - requires dedicated security expertise. Organizations with a DevSecOps team of two to five engineers who can own the platform will extract significantly more value from Aqua than organizations where security is a part-time responsibility shared by developers.
Your compliance framework requires runtime security evidence. Some security certifications and compliance frameworks require evidence of runtime monitoring and anomaly detection, not just pre-deployment scanning. FedRAMP High, some banking regulatory frameworks, and advanced SOC 2 Type II audits increasingly expect runtime security controls. Aqua provides this evidence; Snyk does not.
You are managing dozens of Kubernetes clusters across multiple cloud providers. At this scale, the operational efficiency of having container scanning, Kubernetes security policies, CSPM, and runtime security in a single platform with correlated findings outweighs the higher cost compared to Snyk. When your DevSecOps team needs to understand the security posture of 50 clusters across AWS, Azure, and GCP simultaneously, Aqua’s unified view provides value that individual point tools cannot replicate.
When to Use Both
Some organizations run Snyk and Aqua Security simultaneously, with each tool covering its primary domain:
- Snyk handles developer workflow integration: IDE scanning, PR checks, SCA with reachability analysis, automated fix PRs, and developer-facing vulnerability reporting
- Aqua handles infrastructure security: container image scanning at the registry, Kubernetes admission control, runtime monitoring and enforcement, CSPM, and supply chain security
This dual-tool architecture provides the most comprehensive security coverage but also the highest cost. The overlap in container image scanning creates some redundancy, which most organizations accept as a trade-off. The combined annual cost for a mid-size enterprise could easily exceed $150,000 to $250,000, which justifies a serious evaluation of whether a single platform (Aqua, Prisma Cloud, or another consolidated offering) could cover both needs at lower total cost.
Alternatives to Consider
If neither Snyk nor Aqua Security is the right fit, several alternatives are worth evaluating.
Semgrep is the leading alternative to Snyk Code for SAST. Semgrep’s open-source engine is free with 3,000+ community-maintained rules across 30+ languages. The Semgrep AppSec Platform extends this with SCA reachability analysis, secrets detection, and AI-powered triage at $35/contributor/month. Semgrep’s custom rule authoring capability - using a pattern syntax that mirrors the code you are trying to detect - is more flexible than Snyk Code’s fixed AI engine. For teams that need deep SAST with custom rules, Semgrep is often a better fit. See our Snyk vs Semgrep comparison for details.
Trivy is a free, open-source security scanner from Aqua Security’s own ecosystem (now a CNCF project). It scans container images, file systems, Git repositories, Kubernetes configurations, and SBOM files for known CVEs, misconfigurations, and secrets. For teams that need container image scanning without paying for Snyk or Aqua, Trivy is the strongest free option. It lacks runtime security, developer workflow integration, and AI-powered remediation, but for CI/CD-embedded container scanning, it is genuinely excellent. The fact that Aqua Security created Trivy and open-sourced it speaks to both the strength of the tool and Aqua’s strategy of building goodwill in the developer community.
Prisma Cloud (Palo Alto Networks) is Aqua’s most direct enterprise competitor for cloud-native security. Prisma Cloud has broader cloud coverage (more mature DSPM, stronger CSPM across multi-cloud environments) and the advantage of integration with Palo Alto’s broader security product portfolio. For organizations already in the Palo Alto ecosystem, Prisma Cloud may provide better total value despite comparable pricing to Aqua.
Wiz has emerged as a dominant CSPM and cloud security platform for organizations that prioritize agentless cloud posture management. Wiz’s agentless architecture (no runtime agents required) makes deployment significantly simpler than Aqua’s agent-based model. Wiz provides excellent visibility into cloud misconfigurations and attack paths but does not offer the container runtime enforcement depth that Aqua provides.
Checkmarx is the enterprise SAST alternative to Snyk Code for organizations that need broader language support, deeper taint analysis, and DAST capabilities alongside SAST. Checkmarx One includes SAST, SCA, DAST, API security, IaC scanning, and container scanning in a unified platform. Pricing is similar to Aqua Security - enterprise contracts starting around $40,000 to $60,000 per year. For regulated enterprises that need DAST alongside SAST, Checkmarx addresses a gap that Snyk does not fill. See our Snyk vs Checkmarx comparison for a detailed breakdown.
CodeAnt AI ($24 to $40/user/month) is the right alternative for teams that want developer-facing security scanning with AI-powered code review in a single platform at lower cost than Snyk. CodeAnt AI bundles SAST, secret detection, IaC scanning, AI PR review, and DORA metrics into its Premium plan at $40/user/month. It does not offer the depth of Snyk’s SCA reachability analysis or container scanning, and it has no runtime security capabilities, but for teams evaluating security platforms primarily as developer tools rather than DevSecOps infrastructure, it is a strong contender.
For a broader view of application security platforms, see our best SAST tools roundup and our Snyk alternatives guide.
Final Recommendation
Snyk and Aqua Security are complementary tools that serve different buyers, different security domains, and different organizational maturity levels. Framing the comparison as “which one should I choose” misses the more useful question: “which part of my security program am I trying to build, and which tool serves that need best?”
For developer teams building application security from scratch: Start with Snyk. The free tier, transparent pricing, zero-friction developer onboarding, and comprehensive pre-deployment coverage (SAST, SCA, container image scanning, IaC) give you meaningful security coverage at a cost and complexity level that does not require dedicated DevSecOps infrastructure. Snyk Code’s DeepCode AI engine with IDE integration will catch more security issues that developers actually fix than a sophisticated enterprise platform they never interact with. Pair Snyk with Semgrep if you need custom SAST rules, or with Codacy if you also need code quality gates and technical debt tracking.
For DevSecOps teams managing Kubernetes at scale: Aqua Security deserves serious evaluation, particularly if runtime security and Kubernetes-native admission control are requirements. The operational complexity and cost are real, but for organizations with the maturity to deploy and manage Aqua effectively, its runtime security capabilities are genuinely differentiated. No pre-deployment scanner - Snyk, Semgrep, Checkmarx, or any other - can provide behavioral monitoring and enforcement for running containers. If your threat model includes post-deployment compromise scenarios (and it should), Aqua addresses an attack surface that Snyk leaves uncovered.
For organizations choosing between Snyk and Aqua as a single platform: They are not good substitutes for each other in their respective primary domains. Snyk is better at developer-facing code and dependency security. Aqua is better at container lifecycle security and runtime protection. If you are forced to pick one, choose based on where your most acute security risk lies: code vulnerabilities and dependency exposure (choose Snyk), or deployed container security and runtime threats (choose Aqua). Most mature security programs eventually need both dimensions covered.
The practical path forward for most teams: Implement Snyk (or a comparable developer-facing security tool) first. Get developers scanning code, remediating dependency vulnerabilities, and operating with security feedback in their daily workflow. Once that foundation is in place and you are running containerized workloads at meaningful scale, evaluate runtime security options including Aqua, Falco, and Sysdig. Building developer security habits is harder than deploying infrastructure security tooling, and Snyk’s developer-first design makes that foundation significantly easier to establish.
The security program that catches the most vulnerabilities is not the one with the most sophisticated tools - it is the one where developers are engaged participants rather than passive subjects of security enforcement. Snyk builds that engagement. Aqua Security builds the enforcement layer on top of it.
Frequently Asked Questions
Is Snyk or Aqua Security better for container security?
Aqua Security is generally stronger for container-centric security, particularly for organizations running Kubernetes at scale. Aqua's platform was purpose-built for container runtime security, offering kernel-level enforcement, pod admission controls, cloud workload protection, and behavioral drift detection that Snyk does not match. Snyk Container is solid for pre-deployment image scanning and integrates neatly into developer pipelines, but it does not offer runtime protection or Kubernetes-native policy enforcement. For DevSecOps teams whose primary concern is the container supply chain through to runtime, Aqua is the more complete solution. For development teams that want to shift container security left into the IDE and PR workflow alongside code and dependency scanning, Snyk provides better developer experience.
Does Snyk do runtime security like Aqua?
No. Snyk does not provide runtime security or container runtime protection. Snyk's security coverage is entirely pre-deployment: SAST (source code scanning), SCA (dependency scanning), container image scanning (checking images before they are deployed), and IaC scanning. Aqua Security extends security coverage through deployment and into runtime, with an eBPF-based runtime enforcement agent that monitors running containers, detects behavioral anomalies, and can block malicious activity in real time. This runtime dimension is absent from Snyk's platform and represents a fundamental capability gap. Teams that need runtime protection alongside pre-deployment scanning typically pair Snyk with a runtime security tool, or choose Aqua Security as a more comprehensive alternative.
How much does Aqua Security cost?
Aqua Security does not publish standard pricing on its website. Pricing is custom-quoted based on the number of nodes or workloads, the products selected (Cloud Security, Code Security, Supply Chain Security), and contract length. Industry estimates suggest Aqua pricing starts around $25,000 to $40,000 per year for small deployments and scales to $100,000 to $500,000+ annually for large enterprises with hundreds of nodes and full platform access. Aqua offers a free trial of its CSPM and some container scanning features. For transparent pricing, Snyk's $25 per developer per month Team plan and CodeAnt AI's $24 to $40 per user per month are significantly more accessible starting points for teams without enterprise budgets.
What is Aqua Security used for?
Aqua Security is a cloud-native application security platform used primarily to secure containerized and Kubernetes-based applications throughout their lifecycle. Its core capabilities include container image scanning (detecting known CVEs in base images and packages), IaC security (scanning Terraform, Kubernetes manifests, Helm charts), software supply chain security (detecting malicious packages and dependency tampering), SBOM generation and analysis, cloud security posture management (CSPM) for AWS, Azure, and GCP misconfigurations, Kubernetes-native admission control (blocking non-compliant workloads), and runtime security (monitoring running containers with eBPF-based enforcement). Aqua is used by security and DevSecOps teams at mid-size and large enterprises running complex microservices architectures in cloud environments.
Does Aqua Security do SAST like Snyk?
Aqua Security offers code security as part of its broader platform, but code scanning is not its primary strength. Aqua's code security capabilities are part of the Aqua Code module, which scans source code for vulnerabilities and secrets. However, Aqua's SAST is less mature and less developer-centric than Snyk Code's DeepCode AI engine. Snyk Code provides real-time IDE scanning in VS Code and JetBrains, AI-powered fix suggestions, PR-level feedback with merge gating, and developer-friendly explanations of vulnerabilities. Aqua's code scanning is more oriented toward security team governance than developer workflow integration. Teams that need deep SAST with developer-first ergonomics should choose Snyk Code or a dedicated SAST tool alongside Aqua.
Can I use Snyk and Aqua Security together?
Yes, and this is a reasonable architecture for organizations that need both developer-facing security scanning and runtime protection. In this dual-tool model, Snyk handles SAST, SCA, and developer workflow integration - catching vulnerabilities in source code and dependencies as developers write and commit code. Aqua Security handles container image scanning at the registry level, Kubernetes admission control, runtime protection, and cloud infrastructure security posture. The overlap is primarily in container image scanning, where both tools provide CVE detection. Most organizations that run both tools accept this redundancy in exchange for the coverage each tool provides in its primary domain. The combined cost is significant, which is why some teams evaluate Aqua as a single platform to replace multiple point solutions.
What is the difference between Snyk Container and Aqua Security?
Snyk Container and Aqua Security overlap in pre-deployment container image scanning but diverge significantly beyond that point. Snyk Container scans Docker images for known CVEs in base images and installed packages, integrates with Docker Hub, Amazon ECR, Google Container Registry, and Azure Container Registry, and surfaces findings in the developer workflow alongside code and dependency scanning results. Aqua Security goes further: it provides registry scanning, Kubernetes admission control, runtime protection with eBPF-based behavioral monitoring, network policy enforcement, and drift detection that alerts when a running container deviates from its expected behavior. Snyk Container is a scanning tool. Aqua is a runtime security platform. The difference is pre-deployment visibility versus full lifecycle enforcement.
Which tool is better for compliance - Snyk or Aqua Security?
Both tools address compliance but in different domains. Snyk's Enterprise plan provides compliance reporting mapped to frameworks like PCI DSS, HIPAA, SOC 2, and OWASP, focused on code vulnerabilities and open-source license risk. Aqua Security provides broader compliance coverage across the cloud-native stack: container hardening benchmarks (CIS Kubernetes, Docker CIS), cloud configuration compliance (CIS AWS, CIS Azure), runtime policy enforcement, and SBOM generation required by US Executive Order 14028 and frameworks like SLSA and SSDF. For organizations in regulated industries that need to demonstrate compliance from code through runtime, Aqua's governance capabilities are more comprehensive. For developer-facing compliance evidence in CI/CD and code security audits, Snyk's integration and reporting are more accessible.
Is Aqua Security suitable for small teams?
Aqua Security is primarily designed for mid-size to large enterprises. Its pricing model, sales-driven procurement process, and the operational complexity of deploying and managing its runtime security agents make it a poor fit for teams under 20 to 30 developers or for organizations without a dedicated DevSecOps function. Small teams seeking container security should evaluate Snyk (with a free tier and self-service $25 per developer per month Team plan), Trivy (free open-source container scanning), or Aikido Security (transparent pricing, developer-friendly). Aqua's strength becomes apparent when managing dozens of Kubernetes clusters across multiple cloud providers, which is simply not a small team problem.
Does Snyk offer SBOM generation like Aqua?
Yes, Snyk supports SBOM generation. Snyk can generate SBOMs in CycloneDX and SPDX formats through its CLI and API, documenting all first-party code dependencies scanned by Snyk Open Source. Aqua Security provides SBOM capabilities as part of its supply chain security module, scanning container images, registries, and CI/CD pipelines to generate comprehensive SBOMs that cover the container supply chain beyond just application dependencies. Both tools support the SBOM requirements of US Executive Order 14028. Aqua's SBOM coverage is broader (spanning container layers, base images, and runtime artifacts), while Snyk's SBOM focuses primarily on application-layer dependencies.
What are the best alternatives to Aqua Security?
The best Aqua Security alternatives depend on which capabilities you are replacing. For container image scanning and SCA, Snyk and Trivy (free, open-source) are strong options. For cloud security posture management, Prisma Cloud (Palo Alto Networks), Wiz, and Orca Security are the leading competitors. For Kubernetes-native security, Falco (free, open-source runtime detection) and Sysdig Secure provide alternatives. For a single platform that covers code, container, and cloud security in a more developer-friendly package, Aikido Security provides a modern alternative with transparent pricing. CodeAnt AI at $24 to $40 per user per month is worth considering for teams that want AI-powered code review, SAST, and basic security scanning without the operational complexity of an enterprise platform.
How does Aqua Security compare to Prisma Cloud?
Aqua Security and Prisma Cloud (Palo Alto Networks) are the two leading enterprise cloud-native security platforms. Aqua's strengths are in container and Kubernetes security - its runtime enforcement and supply chain security modules are the most mature in the market. Prisma Cloud has broader coverage, including cloud security posture management across AWS, Azure, and GCP, data security posture management, and integration with Palo Alto's broader security ecosystem. Prisma Cloud has the advantage of Palo Alto's enterprise relationships and brand recognition. Aqua has stronger Kubernetes-native controls and an independent company roadmap. Both are expensive enterprise platforms with similar sales-first pricing models.
Explore More
Tool Reviews
Related Articles
- Checkmarx vs Veracode: Enterprise SAST Platforms Compared in 2026
- Codacy vs Checkmarx: Developer Code Quality vs Enterprise AppSec in 2026
- Codacy vs Snyk: Code Quality Platform vs Developer Security Platform (2026)
- DeepSource vs Coverity: Static Analysis Platforms Compared (2026)
- DeepSource vs Snyk: Code Quality Platform vs Developer Security Platform (2026)
Free Newsletter
Stay ahead with AI dev tools
Weekly insights on AI code review, static analysis, and developer productivity. No spam, unsubscribe anytime.
Join developers getting weekly AI tool insights.
Related Articles
Checkmarx vs Veracode: Enterprise SAST Platforms Compared in 2026
Checkmarx vs Veracode - enterprise SAST, DAST, SCA, Gartner positioning, pricing ($40K-250K+), compliance, and when to choose each AppSec platform.
March 13, 2026
comparisonCodacy Free vs Pro: Which Plan Do You Need in 2026?
Codacy Free vs Pro compared - features, limits, pricing, and when to upgrade. Find the right Codacy plan for your team size and workflow.
March 13, 2026
comparisonCodacy vs Checkmarx: Developer Code Quality vs Enterprise AppSec in 2026
Codacy vs Checkmarx - developer code quality vs enterprise AppSec, pricing ($15/user vs $40K+), SAST, DAST, SCA, compliance, and when to choose each.
March 13, 2026
 Snyk Code Review
Snyk Code Review